Table of Contents
, there are a number of factors to look for, consisting of debt monitoring, identification monitoring, identification burglary recovery and insurance coverage and even more. They look for signs of identity theft, such as sudden score motion and unexpected credit queries. When they see these indicators, they signal the individual so they can take action and file a record.
In addition to that, the policy may have a deductible or other exclusions or limitations; most do not cover any individual already covered by renters or house owners insurance coverage, which is why it is very important to always read the great print - learn more. If your house owners or occupants insurance coverage already covers identification theft, then the insurance policy from your identity theft protection solution might not use
An Unbiased View of Identity Protection Tools
: Finally, we take a look at where the company is based to see what surveillance laws it falls under. For firms based in the United States, they might be required to share consumer data as a result of the U.S's subscription in 5 Eyes, 9 Eyes and 14 Eyes. This will just take place in rare cases.

Yes, a person can take your identification with your government-issued ID or driver's license. Any type of records which contain Personally Identifiable Information (learn more) (PII) including your complete name, home address, day of birth, image or even your trademark can be used to steal your identity and target you with phishing rip-offs. Continue analysis to learn what a person can do with your ID, exactly how to tell if a person is utilizing your ID, what to do if your ID is shed or taken and just how to maintain your ID safe.
Imagine your chauffeur's certificate number becomes compromised and comes under the hands of a person who makes duplicates of your ID and after that offers them to lawbreakers. If a criminal obtains captured for any type of crime with your ID, regulation enforcement might place those costs on your document instead of their own. This scenario is really unsafe since it will be challenging to verify that you really did not dedicate those crimes given that an additional individual has your ID.
Things about Identity Protection Tools
If someone has your ID, they can use your complete name to look you up and discover your e-mail address or contact number. Once they have ways to call you, somebody can send you a counterfeit message concerning dubious activity in your checking account or an issue with a social networks account.
You can tell if somebody is utilizing your shed or swiped ID for harmful purposes by seeing the following: A brand-new funding or credit line that you did not accredit shows up on your credit rating record, suggesting that someone has actually utilized your ID to devote scams You can not log in to your online accounts, suggesting that somebody utilized your ID and details associated with your ID to jeopardize your accounts You stop receiving mail, which might be an indicator somebody has actually modified the address on your ID to match theirs You start getting calls from financial obligation enthusiasts concerning financial obligation that isn't your own, indicating someone has utilized your ID to impersonate you and been accepted for credit history cards or financings Your bank alerts you of illegal task, which indicates someone has actually used your ID to withdraw huge amounts of cash or make unapproved deals There are several things you should do if your ID has actually been lost or stolen, such as reporting the loss or theft to your state's DMV, cold your debt and filing a report with the Federal Profession Payment (FTC).
You ought to report your ID as taken - click here to the Federal Trade Commission (FTC), which will certainly utilize the information you offer to team up with legislation enforcement in exploring your identification theft. It is very important to submit a record with the FTC as soon as possible so the FTC can share your experience with law enforcement to aid recoup your identification and make use of the info from your situation to aid protect others
Our technology group has years of experience with LifeLock, and we have ended up being exceptionally knowledgeable about what they offer. Their most thorough plan, Ultimate And also, offers extensive protection and identification burglary resolution services that need to cover the requirements of many elders. We obtained text, phone, and mobile app alerts whenever there was a feasible data breach or abuse of our personal information.
Facts About Identity Protection Tools Uncovered
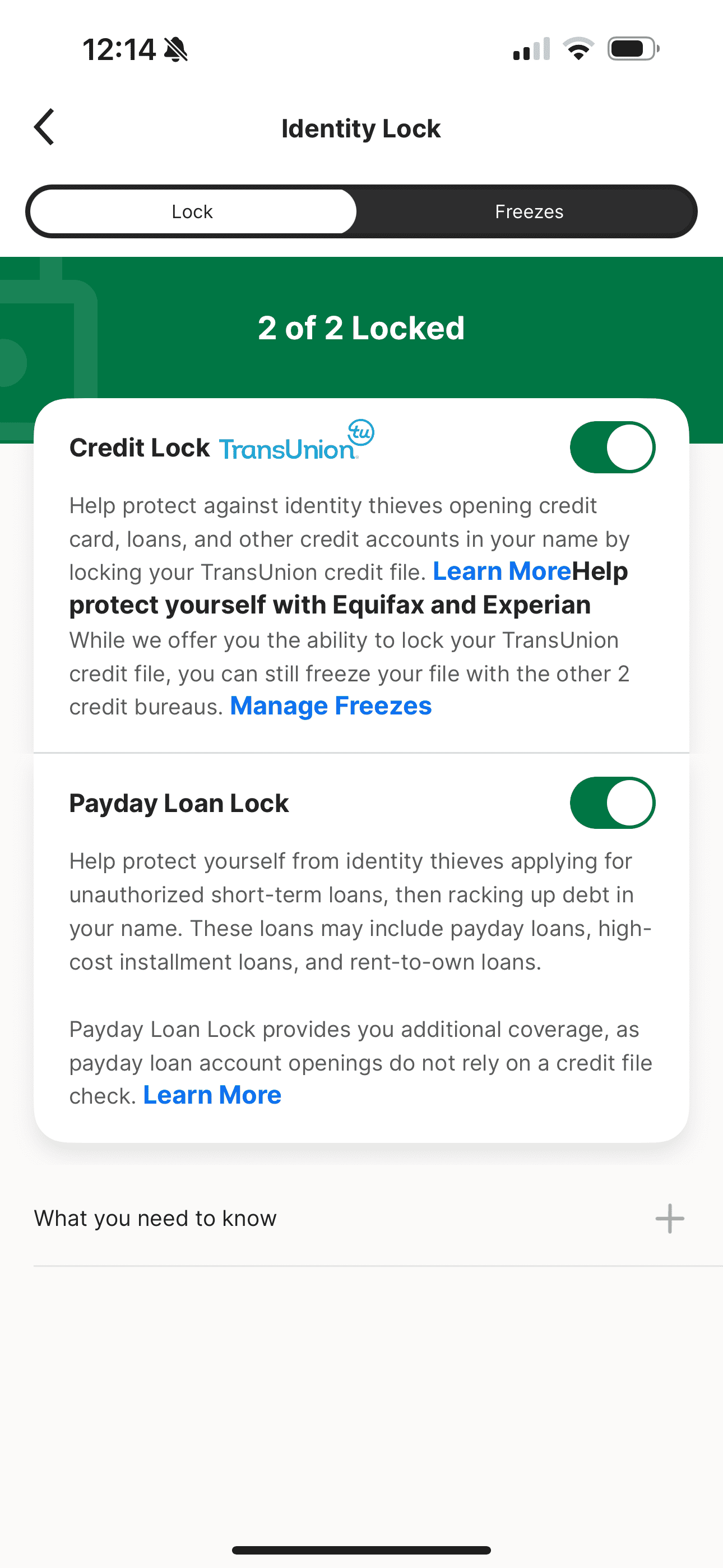
Not all LifeLock strategies, nevertheless, offer the same degree of protection. The Standard plan is somewhat very little in its offerings, but you can still rise to $1.05 million in identification burglary insurance, together with Social Safety and security number, credit rating, and monetary tracking. If you're out a tight spending plan, you can get more features with among the costlier strategies, such as: Insurance coverage for up to 2 adults As much as $1 numerous protection for lawful fees (per grownup) Up to $1 million in individual expense compensation (per adult) As much as $1 million in stolen funds reimbursement (per grownup) Approximately $3 million in overall insurance coverage Three credit bureau monitoring Payday advance loan lock to quit fraudulent high-interest financings Notifies for criminal activities dedicated in your name Social network tracking Financial and financial investment account surveillance Telephone number security Home title tracking LifeLock features 3 identity burglary security plans ranging from $11 - learn more.99 to $69.99 per month for the initial year of service

The Requirement strategy, for instance, sets you back $89.99 for the very first year, and after that $124.99 for each year after that. With the addition of antivirus services and high repayment quantities, though, LifeLock's price is rather sensible.
Navigation
Latest Posts
Some Ideas on Identity Protection Tools You Need To Know
The Best Strategy To Use For Identity Protection Tools
The smart Trick of Identity Protection Tools That Nobody is Discussing